Security
18 articles tagged with Security.

Observability vs Monitoring: Technical Differences Explained
Discover the key observability vs monitoring: technical differences, including telemetry, tools, and use cases that differentiate these vital DevOps practices.

What is Configuration Drift?
What is Configuration Drift? Learn causes, risks, and best practices to detect, prevent, and fix drift with IaC and GitOps.

What is Metamorphic Testing?
What is Metamorphic Testing? Discover how it solves the test oracle problem and how to test complex AI, APIs, and untestable code.

What is Mutation Testing?
What is mutation testing? Just break your code! Learn how mutants reveal weaknesses and strengthen your automated tests.

How Debuggers Know What to Show You?
Learn how debuggers know what to show you? (program slicing) with examples of static vs dynamic slicing and dependency graphs for faster debugging.
What Is Chaos Engineering?
Discover what is chaos engineering and how proactive failure testing builds stronger, more reliable systems. Learn the principles and tools.
Authorization: RBAC vs ABAC
The core difference between RBAC and ABAC boils down to one thing: how they determine permissions. RBAC is static whereas ABAC is dynamic.
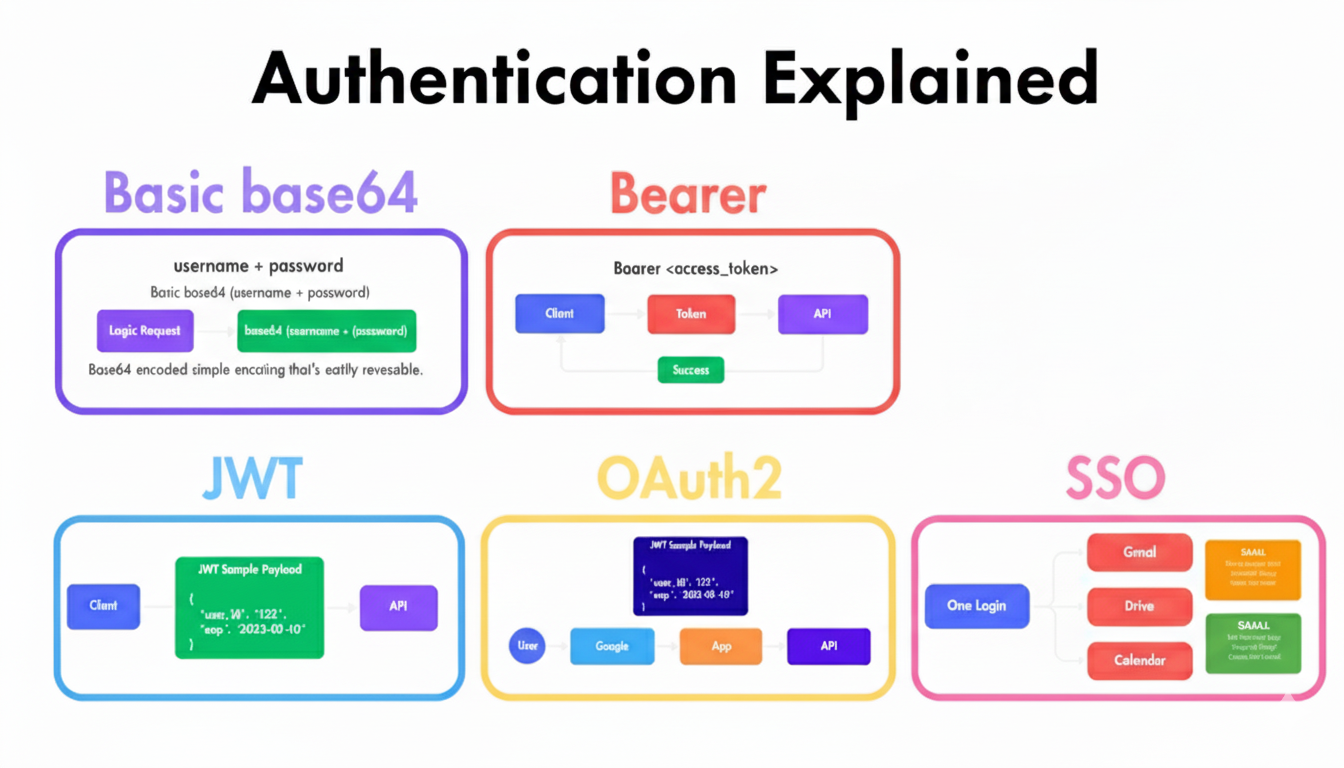
Authentication Explained: Basic, Bearer, OAuth2, JWT & SSO
This guide will break down five common methods: Basic, Bearer, OAuth2, JWT, and SSO. We'll look at how each one works.
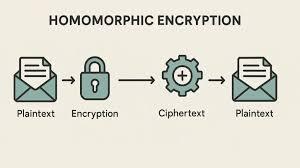
What is Homomorphic Encryption? A Practical Guide with Examples
Homomorphic encryption is a powerful form of cryptography that allows computation on data while it remains encrypted.

Authentication & Access Control
You sign in to your bank account and can only view your balance. The bank manager logs in and can approve loans. Same system, different powers but how does the app decide?

Encryption vs Tokenization: Which Data Security Method Is Better?
When you're trying to decide between encryption vs tokenization, it helps to think in analogies. Encryption is like locking your valuables in a high-tech safe, the data is still there, just scrambled into an unreadable format. Only someone with the right key can open it.
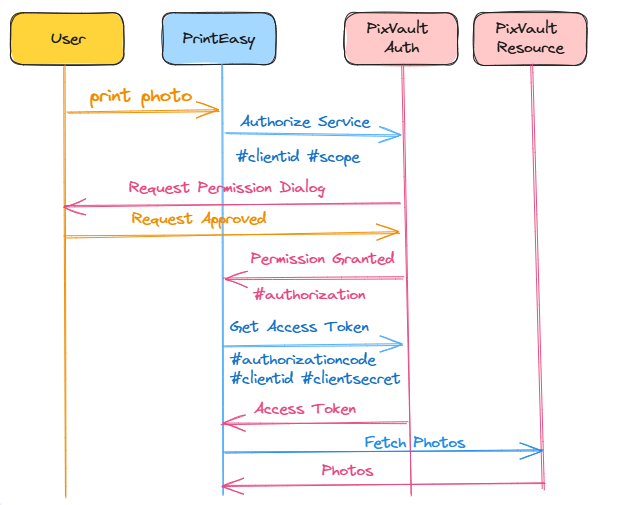
EP 37: What is OAuth?
OAuth is an open standard protocol that allows users to grant apps access to their data without sharing their passwords.
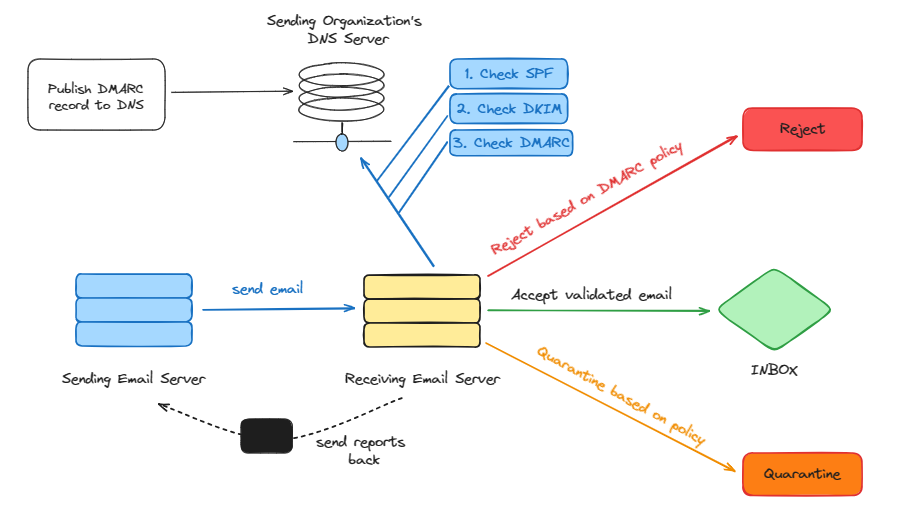
EP 25: What is DMARC Record? Why is it used?
DMARC prevents email spoofing and phishing by authenticating email senders.
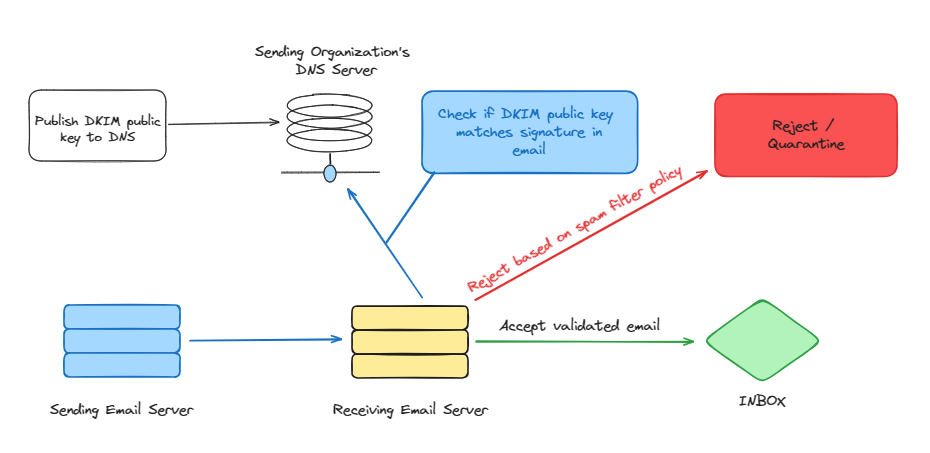
EP 24: What is DKIM Record? Why is it used?
DKIM is an email authentication protocol that enhances email security by preventing domain-based phishing attacks.
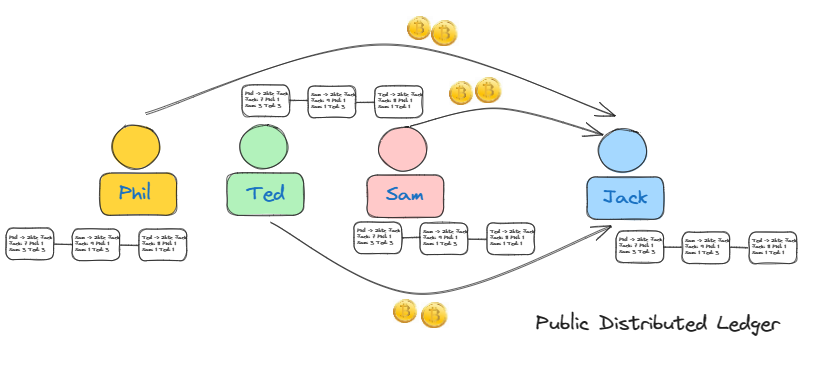
What is Blockchain?
Blockchain is a decentralized ledger technology that records transactions securely in an immutable chain of blocks.
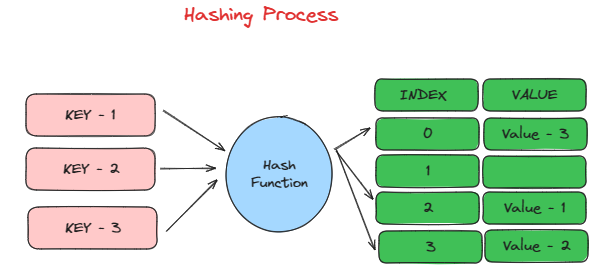
What is hashing and what different types are there?
Hashing is a way to convert data into a shorter code for secure storage or comparison.

What is Encryption and what different types are there?
How are we protected on the internet when everyone is trying to get our data?
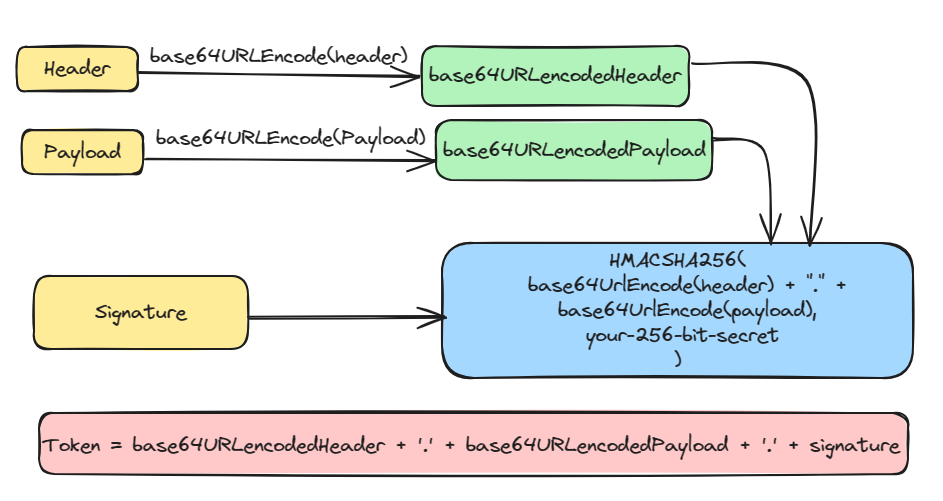
What the hell are JWT tokens?
Everyone is talking about them, but what are they?